An Overview of the Information System Audit
In the digital era, information systems form the backbone of organizational operations, decision-making, and regulatory compliance. With increasing dependence on technology, risks relating to data security, system failures, cyber threats, and regulatory non-compliance have significantly increased. In this context, Information System Audit (ISA) has emerged as a crucial mechanism to ensure the integrity, reliability, security, and lawful functioning of information systems.
Information System Audit plays a vital role in strengthening internal controls, protecting sensitive data, ensuring compliance with applicable laws, and supporting corporate governance. It provides assurance to management, regulators, and stakeholders that the organization’s information systems are adequately controlled and aligned with business objectives.
What is Information System Audit?
Information System Audit is a systematic and independent examination of an organization’s information systems, technology infrastructure, policies, and operations to evaluate whether they ensure data integrity, confidentiality, availability, and compliance with legal and regulatory requirements.
In simple terms, an Information System Audit assesses whether:
- Information systems are secure and reliable,
- Data is accurate, complete, and protected,
- Internal controls are effective, and
- Technology usage complies with applicable laws, standards, and organizational policies.
Unlike financial audits, which focus on financial records, Information System Audit focuses on technology controls, data security, system efficiency, and compliance risks.
Types of Information System Audit
- Systems and Application Audit
Systems and Application Audit focus on the evaluation of specific software applications and the systems that support business operations. The primary objective of this audit is to ensure that applications function accurately, reliably, and in accordance with defined business requirements.
This type of audit examines whether:
- Application controls are properly designed and implemented
- Data input, processing, and output are accurate and complete
- Access to applications is restricted to authorized users
- Errors, exceptions, and unauthorized transactions are adequately detected and controlled
Systems and Application Audit is particularly important for applications handling critical functions such as accounting, payroll, inventory management, and customer data, as errors or manipulation in such systems may result in financial loss or legal non-compliance.
- Infrastructure Audit
Infrastructure Audit involves a detailed review of an organization’s IT infrastructure, including hardware, network components, servers, operating systems, and communication facilities. The objective of this audit is to ensure that the infrastructure adequately supports business operations and is secure, reliable, and scalable.
This audit assesses:
- Adequacy and configuration of hardware and network systems
- Reliability and performance of servers and operating systems
- Network security measures such as firewalls and intrusion detection systems
- System availability and capacity planning
Infrastructure Audit helps in identifying weaknesses such as outdated systems, inadequate network security, or poor system maintenance, which may expose the organization to operational disruptions or cyber risks.
- Security Audit
Security Audit is one of the most critical forms of Information System Audit, as it focuses on the protection of information assets against unauthorized access, data breaches, and cyber threats. The main aim is to ensure the confidentiality, integrity, and availability of data.
This audit examines:
- Access control mechanisms and user authentication procedures
- Data encryption and secure transmission practices
- Cybersecurity policies and incident response mechanisms
- Protection against malware, hacking, and data leakage
Security Audit is essential for ensuring compliance with data protection laws and for safeguarding sensitive personal, financial, and business information.
- Compliance Audit
Compliance Audit focuses on verifying whether the organization’s information systems comply with applicable laws, regulations, contractual obligations, and industry standards. It ensures that IT operations are aligned with statutory and regulatory requirements.
This type of audit evaluates compliance with:
- Information Technology laws and data protection regulations
- Industry-specific regulatory guidelines
- Internal IT policies and standard operating procedures
- International standards such as ISO or other prescribed frameworks
Compliance Audit is particularly significant for regulated entities, as non-compliance may result in penalties, legal action, and reputational damage.
- Operational IT Audit
Operational IT Audit examines the efficiency, effectiveness, and economy of an organization’s IT operations. The objective is to determine whether IT resources are being utilized optimally to support business objectives.
This audit reviews:
- IT service management processes
- System performance and downtime management
- Resource utilization and cost efficiency
- Alignment of IT strategy with organizational goals
Operational IT Audit helps management identify areas for improvement, reduce operational inefficiencies, and enhance the overall performance of IT functions.
Process of conducting Information System Audit
The process of conducting Information System Audit is as follows:
- Opening Meeting
The audit process begins with an opening meeting between the auditors and management to discuss the scope, objectives, timelines, and expectations of the audit. - Scheduling of Audit Program
An audit plan and program are prepared, outlining audit areas, timelines, responsibilities, and information requirements. - Assessing Business Systems and Processes
Auditors review the organisation’s business systems, workflows, and operational processes to understand how activities are carried out. - Testing Internal Controls
Key internal controls are tested to evaluate their design, effectiveness, and implementation across financial and operational areas. - Discussion with Management on Audit Findings
Preliminary audit observations are discussed with management to validate findings, understand root causes, and obtain clarifications. - Preparation of Draft Audit Report
A draft audit report is prepared, highlighting observations, risks, control gaps, and recommended corrective actions. - Release of Final Audit Report
After incorporating management responses, the final audit report is issued to the Board or relevant stakeholders. - Closing Meeting
A closing meeting is held to formally conclude the audit, discuss key findings, and agree on timelines for corrective actions. - Follow-up of Audit Compliance
Post-audit follow-up is conducted to ensure implementation of recommended actions and compliance with audit observations.
Elements of IS audit
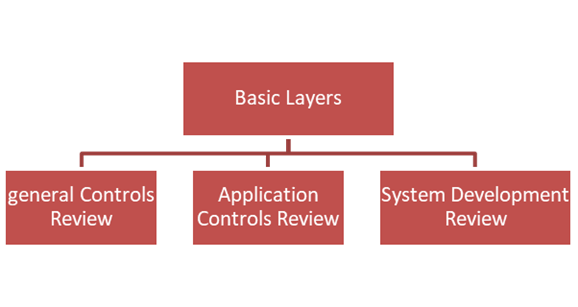
1. General Control Review
A review of the controls which govern the development, operation, maintenance, and security of application systems in a particular environment. This type of audit might involve reviewing a data center, an operating system, a security software tool, or processes and procedures such as the procedure for controlling production program changes etc.
2. Application Controls Review
A review of controls for a specific application system that would involve an examination of the controls over the input, processing, and output of system data. Data communications issues, program and data security, system change control, and data quality issues are also considered.
3. System Development Review
A review of the development of a new application system that involves an evaluation of the development process as well as the product. Consideration is also given to the general controls over a new application, particularly if a new opening environment or technical platform will be used.
Conclusion
To make sure that an organization’s information systems are safe, dependable, effective, and compatible with legal and regulatory standards, an information system audit is essential. Data integrity, fraud prevention, and operational risk reduction are all aided by the audit’s methodical assessment of controls, risk management procedures, and system operations.
An effective information system audit strengthens IT governance and advances organizational goals by pointing out flaws and control gaps as well as offering doable suggestions for enhancement. As a result, information system auditing is a crucialinstrument for efficient information system management, accountability, and ongoing development.















